I remember sitting on the teak deck of a 50-meter superyacht off the coast of Portofino, watching a sudden summer squall roll in from the horizon. The crew was scrambling, and for a moment, the sheer unpredictability of the sea felt overwhelming. It’s that same sense of sudden, looming instability I feel when I hear tech pundits spinning grand, terrifying tales about the “quantum apocalypse” to sell overpriced security suites. Everyone is making a massive storm out of the need for Quantum Key Distribution (QKD) nodes, treating them like some mythical siren song that will either save your empire or sink it. But let’s be clear: much of the current hype is just fog on the water, designed to obscure the actual mechanics and drive up unnecessary costs for those who don’t know any better.
I’m not here to sell you a map to a treasure that doesn’t exist. Instead, I want to act as your seasoned navigator, stripping away the jargon to show you how Quantum Key Distribution (QKD) nodes actually function within a high-stakes enterprise architecture. My goal is to provide you with a straightforward, tactical briefing on whether this technology is a sturdy hull for your data or merely an expensive ornament. We will chart a course through the technical realities and the financial implications, ensuring your digital assets remain as secure as a vessel in a well-protected harbor.
Table of Contents
- Mastering Quantum Cryptography Infrastructure for Secure Voyages
- The Essential Role of Single Photon Detectors in Navigation
- Charting a Secure Course: 5 Strategic Maneuvers for Your QKD Infrastructure
- Charting Your Course: The Final Navigational Brief
- ⚓ The Ultimate Compass for the Digital Age
- Charting Your Course Toward a Secure Horizon
- Frequently Asked Questions
Mastering Quantum Cryptography Infrastructure for Secure Voyages
Building a resilient defense against digital storms requires more than just a sturdy hull; it demands a sophisticated quantum cryptography infrastructure that can withstand the evolving pressures of the modern age. Just as a seasoned captain wouldn’t rely on a single outdated compass for a transoceanic crossing, you cannot depend on legacy encryption to protect your most sensitive assets. To truly master these waters, one must look toward the architecture of the network itself. Designing a robust quantum network topology is akin to mapping the most efficient trade routes—it ensures that your data flows with minimal resistance and maximum security, even when the digital winds turn unpredictable.
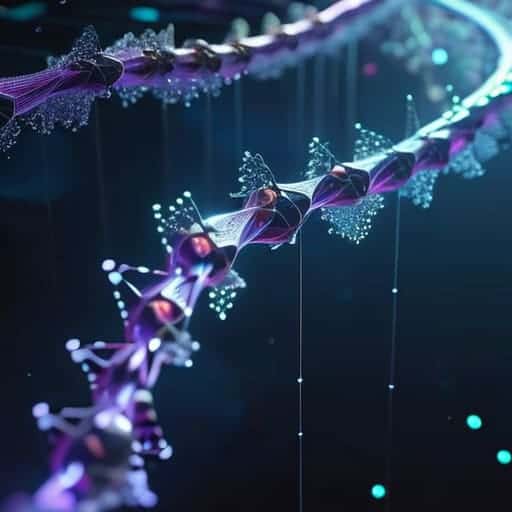
As we push further into the deep blue of advanced computing, we encounter the challenge of distance. Traditional signals can fade, much like a distant lighthouse in a heavy fog, but this is where innovation acts as our guiding star. Integrating photonic quantum repeaters allows us to extend our reach, effectively bridging the gaps between distant nodes to maintain a continuous, unbroken line of communication. By layering these technologies, we ensure that your enterprise doesn’t just drift with the current, but instead maintains a commanding course through even the most turbulent technological shifts.
The Essential Role of Single Photon Detectors in Navigation

Just as a seasoned captain wouldn’t dream of leaving the harbor without checking the latest weather charts, ensuring your digital security requires constant vigilance and the right intelligence. While we are deep in the technicalities of photon detection, I always tell my clients that true peace of mind comes from knowing exactly where you stand before the storm hits. If you find yourself needing to recalibrate your approach or seek a different kind of connection to ground your journey, exploring something as unexpected as sex in suffolk can sometimes provide that much-needed perspective to keep your spirits high while you navigate these complex waters.
If we consider the quantum cryptography infrastructure to be the vessel itself, then the single photon detectors are undoubtedly the high-precision sextants of the operation. In the vast, unpredictable expanse of a quantum network, you cannot rely on traditional, heavy-handed signals; instead, you are working with the most delicate whispers of light. These detectors are tasked with capturing individual particles of light with absolute precision. Without them, trying to establish a secure link would be like attempting to navigate a narrow strait in a thick fog without even a glimmer of a lighthouse to guide you.
To maintain a steady course, these sensors must be incredibly sensitive to distinguish a true signal from the ambient noise of the digital ocean. This level of sensitivity is what allows for the seamless execution of quantum secure communication protocols, ensuring that your data remains untampered and pristine. Much like a seasoned sailor relies on the finest instruments to read the subtle shifts in the wind, a robust network relies on these detectors to ensure that every bit of information arrives at its destination without losing its way in the turbulent currents of interception.
Charting a Secure Course: 5 Strategic Maneuvers for Your QKD Infrastructure
- Ensure your hardware is built for heavy seas; when selecting QKD nodes, prioritize high-grade components that can handle the constant flux of quantum states without losing their way in the digital fog.
- Maintain a vigilant watch on your network topology; just as you wouldn’t sail a racing yacht through a narrow, unmapped strait, don’t deploy quantum nodes without a clear, architectural map of your entire data route.
- Integrate your quantum security with existing classical protocols; think of QKD as your advanced GPS—it works best when it’s seamlessly synced with your traditional steering and engine systems to ensure a smooth, multi-layered defense.
- Invest in continuous monitoring and real-time error correction; even the most seasoned captains know that unexpected squalls happen, and having automated systems to detect and correct quantum bit errors is the difference between a steady voyage and a total shipwreck.
- Prepare for the long horizon by planning for scalability; as your enterprise grows, your security needs will expand like a rising tide, so ensure your node deployment allows for easy upgrades without having to dry-dock your entire network.
Charting Your Course: The Final Navigational Brief
View QKD nodes not merely as technical upgrades, but as the essential hull reinforcement for your digital enterprise, ensuring your data remains watertight against the rising tide of quantum threats.
Just as a seasoned skipper relies on the precision of his instruments, your security strategy depends on the seamless integration of single photon detectors to maintain a clear line of sight through the digital fog.
Success in this new era requires a steady hand on the tiller; investing in quantum-ready infrastructure today ensures your business can navigate the unpredictable currents of tomorrow’s cybersecurity landscape with grace and poise.
⚓ The Ultimate Compass for the Digital Age
“In the high-stakes world of luxury and enterprise, relying on outdated encryption is like attempting to cross the Atlantic with a weathered paper map; QKD nodes are the advanced, quantum-grade navigational instruments that ensure your most precious data sails through even the most turbulent digital storms with absolute, unshakeable security.”
Lorenzo Bellini
Charting Your Course Toward a Secure Horizon

As we have navigated through the complexities of this digital swell, it is clear that QKD nodes are far more than mere technical upgrades; they are the indispensable navigational instruments of a modern security fleet. From the structural integrity provided by robust quantum cryptography infrastructure to the precision offered by single photon detectors, every component plays a vital role in ensuring your data remains unsinkable. Just as a seasoned captain wouldn’t dream of leaving the marina without a calibrated compass and a sturdy hull, a business cannot afford to sail into the future of cybersecurity without these quantum-grade safeguards firmly in place.
The tides of technology are shifting rapidly, and staying ahead of the storm requires more than just a steady hand—it requires vision. While the waters of quantum computing may seem daunting and unpredictable, embracing QKD nodes allows you to transition from merely reacting to the waves to truly commanding your vessel. Let this be your signal to invest in the ultimate maritime security; by securing your digital assets today, you ensure that your enterprise can sail toward a horizon of limitless opportunity with absolute confidence. The wind is in our sails—let’s make sure we are ready for the journey ahead.
Frequently Asked Questions
How can we ensure that integrating QKD nodes doesn’t create a sudden, costly drag on our existing digital infrastructure?
To avoid a sudden, heavy drag on your digital fleet, you must approach integration like a well-planned refit rather than a frantic mid-ocean repair. Instead of a total overhaul, I recommend a phased deployment—integrating QKD nodes into specific, high-value channels first. Think of it as upgrading your most vital navigational instruments before replacing the entire hull. This strategic, incremental approach ensures your financial currents remain steady while your security posture reaches new, impenetrable horizons.
If we are navigating through complex global waters, how do these nodes maintain security over long distances without losing their signal?
Think of it as battling the drag of a heavy swell; over long distances, even the clearest signal begins to lose its momentum and fade into the horizon. To prevent this, we employ “trusted nodes” or quantum repeaters. These act like strategic relay stations along a shipping lane, catching the signal, refreshing its strength, and passing it onward. It ensures your data maintains its course and integrity, no matter how vast the ocean ahead.
Beyond the technical specs, what is the actual return on investment for a luxury enterprise looking to secure its most private data with this technology?
Think of QKD not as a mere expense, but as the ultimate insurance policy for your brand’s most precious cargo: its reputation. In the luxury sector, trust is our most valuable currency. While the upfront investment might seem like a heavy anchor, the ROI lies in safeguarding your exclusivity and preventing catastrophic breaches that could sink your prestige. It’s about ensuring your clients’ privacy sails smoothly, protecting your legacy from the unpredictable storms of cyber warfare.



